Dependency Check
安裝 Dependency-Check
下載執行檔
https://owasp.org/www-project-dependency-check/
下載後,解壓縮
tar -xvf dependency-check-12.1.0-release.zip如:解壓縮到 c:\tools\dependency-check
備註:也可透過如Maven Plugin,透過 Maven 下載
參數說明
Windows
dependency-check.bat --project "My App Name" --scan "c:\java\application\lib"*nix
dependency-check.sh --project "My App Name" --scan "/java/application/lib"To view the command line arguments, see the arguments page
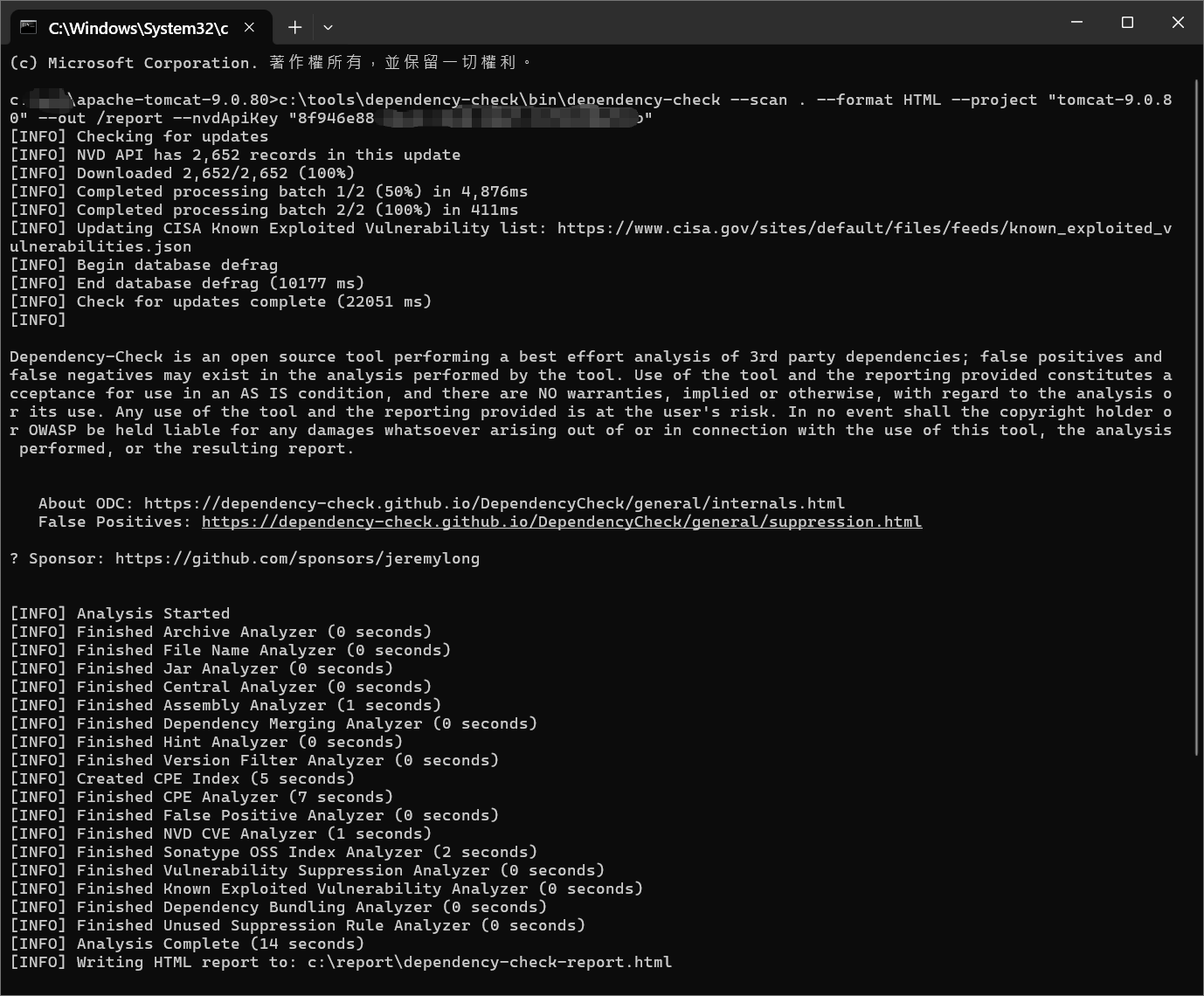
執行
透過命令列執行:
c:\tools\dependency-check\bin\dependency-check --scan . --format HTML --project "abc-project" --out /report --nvdApiKey "YOUR_NVD_API_KEY"| 短參數 | 參數名稱 | 參數格式 | 說明 | 是否必要 |
|---|---|---|---|---|
| –project | project | <name> |
專案名稱,會顯示在掃描報告中。 | 選填 |
| -s / –scan | scan | <path> |
掃描路徑,可多次指定。支援 Ant 格式路徑(如 'directory/**/*.jar'),建議使用單引號以避免 shell 替換(參考 issue #1812)。 |
通常必填 |
| -f / –format | format | <format> |
輸出格式,可指定多個格式(HTML、XML、CSV、JSON、JUNIT、SARIF、JENKINS、GITLAB、ALL),預設為 HTML。 | 選填 |
| -o / –out | out | <path> |
輸出報告的資料夾路徑,預設為目前目錄。若格式非 ALL,可指定檔案名稱。 | 選填 |
| –nvdApiKey | nvdApiKey | <apiKey> |
用於存取 NVD API 的金鑰,可由 https://nvd.nist.gov/developers/request-an-api-key 申請。 | 選填 |
NVD API 金鑰
NVD API 的金鑰,可由 https://nvd.nist.gov/developers/request-an-api-key 申請 在執行時,如使用 API KEY,下載速度,會快於沒使用 API KEY 在執行時,NVD的資料庫,也會有更新,並會存放於dependency-check的data資料夾中
執行範例
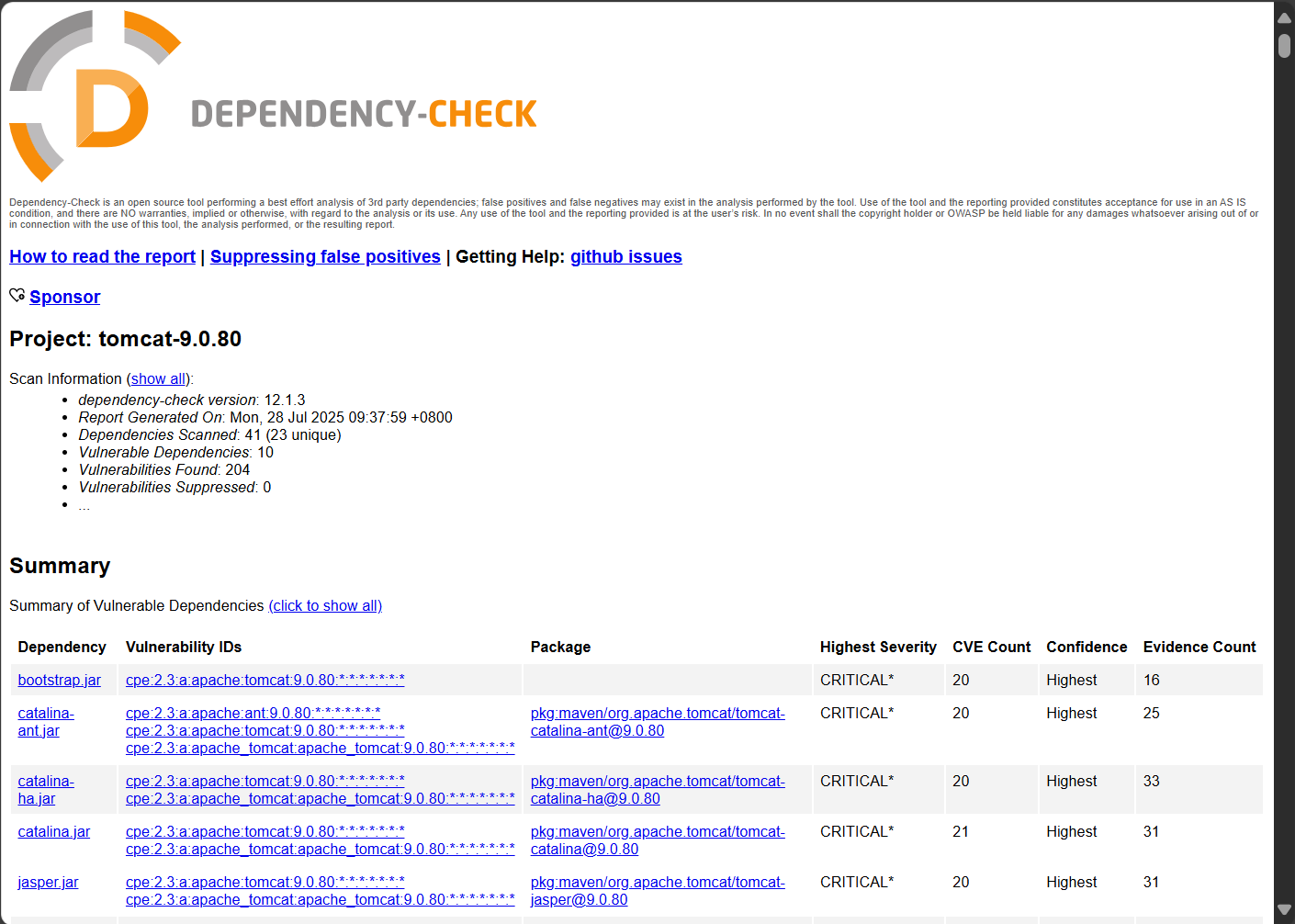
sample report
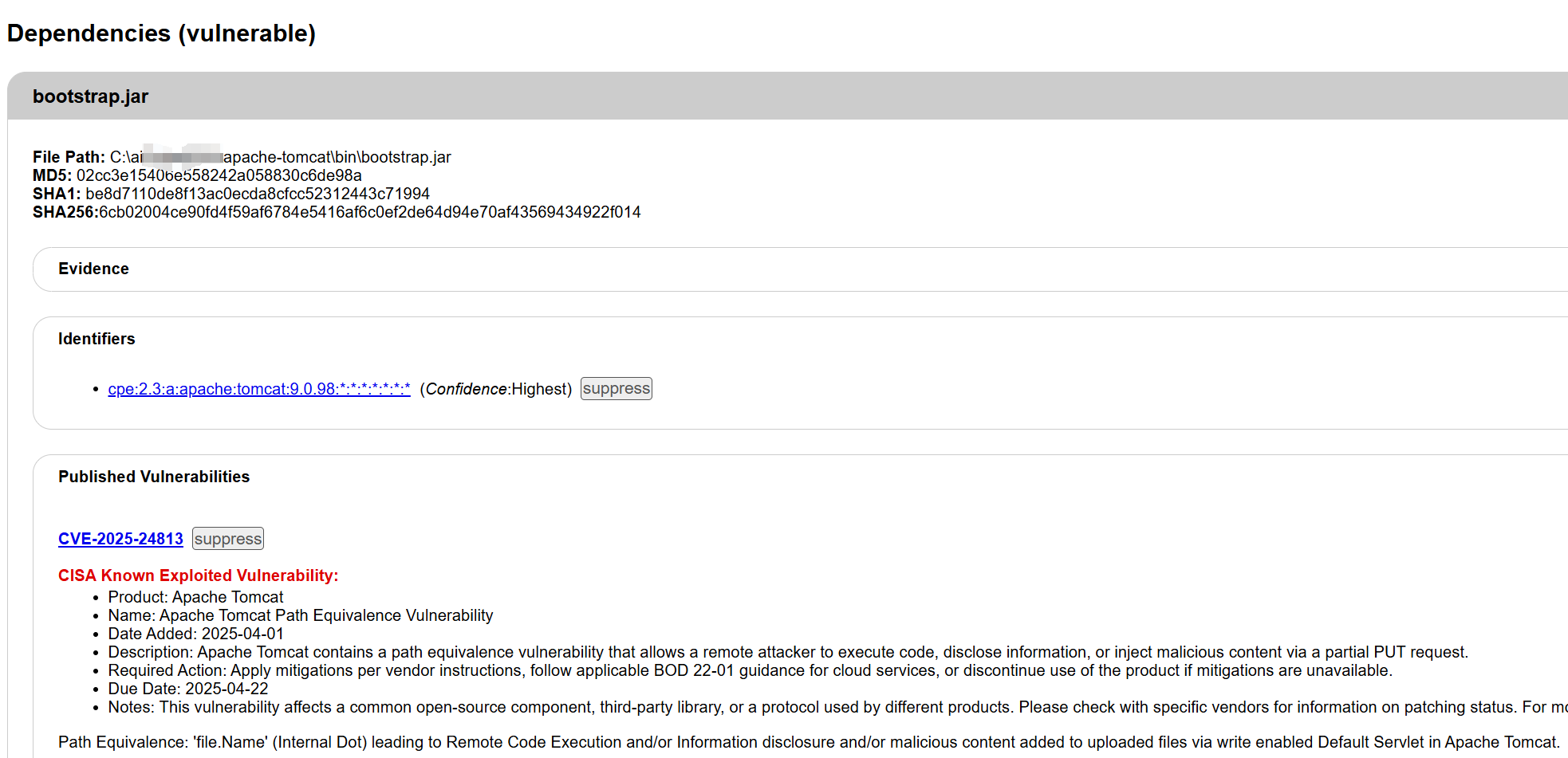
bootstrap.jar
至檔案目錄下,可檢查 bootstrap.jar 的 Manifest 資訊 其為 org.apache.catalina.startup.Bootstrap 版本為 9.0.80
Manifest-Version: 1.0
Ant-Version: Apache Ant 1.10.15
Created-By: 17.0.13+11 (Eclipse Adoptium)
Main-Class: org.apache.catalina.startup.Bootstrap
Specification-Title: Apache Tomcat Bootstrap
Specification-Version: 9.0
Specification-Vendor: Apache Software Foundation
Implementation-Title: Apache Tomcat Bootstrap
Implementation-Version: 9.0.80
Implementation-Vendor: Apache Software Foundation
X-Compile-Source-JDK: 8
X-Compile-Target-JDK: 8
Class-Path: commons-daemon.jarreport
在 report 中,可以看到其版本有高信心值的風險 Identifiers cpe:2.3:a:apache:tomcat:9.0.80:::::::* (Confidence:Highest)
漏洞
並在report中,看到多個漏洞的狀況
Published Vulnerabilities CVE-2025-24813 suppress
CISA Known Exploited Vulnerability: Product: Apache Tomcat Name: Apache Tomcat Path Equivalence Vulnerability Date Added: 2025-04-01 Description: Apache Tomcat contains a path equivalence vulnerability that allows a remote attacker to execute code, disclose information, or inject malicious content via a partial PUT request. Required Action: Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. Due Date: 2025-04-22
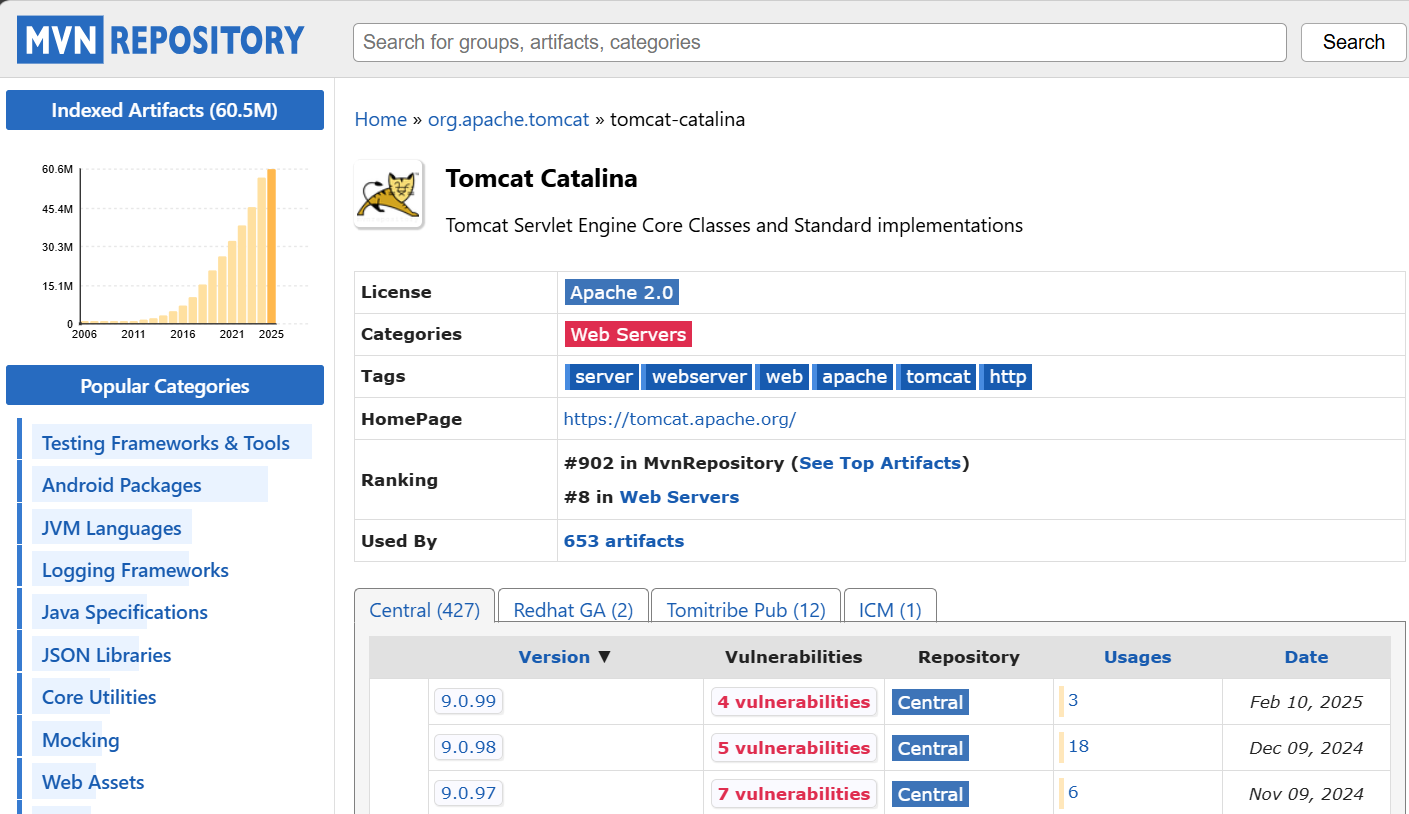
查詢 Maven
以Class name查詢 Maven https://mvnrepository.com/artifact/org.apache.tomcat/tomcat-catalina
Tomcat Catalina 9.0.80 版本
應下載最新的元件